TrustFLEX Platform
Pre-Configured Security ICs to Support the Most Common Authentication Use Cases
If you find yourself on this page, you’ve most likely already reviewed the features of the Trust&GO platform and have determined that you need a more flexible option to implement security ICs in your design. With our TrustFLEX platform, you can order a variety of security ICs with a pre-established locked configuration that supports the most common embedded security use cases. The TrustFLEX platform supports secure authentication ICs, 32-bit microcontrollers and platform root of trust ICs.

Select a TrustFLEX-Compatible Device
Trust Shield Family Updates Registration
We are expanding our platform root of trust portfolio with the Trust Shield family, including TS1800 and TS50x controllers designed for post‑quantum‑ready secure boot and platform resiliency aligned with NIST SP 800‑193 and OCP requirements.
We are working with leading industry customers ahead of release, with general availability and TrustFLEX enablement forthcoming. Register to receive updates and request priority access to product resources.
Tools, documentation and TrustFLEX configurations will be available at general availability.

TA101 TrustMANAGER and TrustFLEX Early Adopter Program
Get early access to TA101‑TFLX (TrustFLEX) and TA101‑TMNG (TrustMANAGER) beta silicon devices.
TA101‑TFLX is a robust secure key storage device paired with a set of predefined security protocols for teams who want to integrate TA101 into their own public key infrastructure (PKI) systems.
TA101‑TMNG includes the same key storage and protocol capabilities, but adds the keySTREAM cloud platform for remote configuration, PKI creation, key management and firmware updates—removing the burden of building a managed IoT security infrastructure in‑house.

Choose From These TrustFLEX Use Cases
- AWS® IoT authentication
- Microsoft® Azure® authentication
- TLS
- Wireless Power Consortium (WPC) Qi® 1.3 and 2.0 wireless power charging authentication
- Certificate authentication for any Public Key Infrastructure (PKI) or cloud platform
- Token authentication
- Secure boot
- Over-the-Air (OTA) verification
- Firmware IP protection
- Code rollback
- Hardware attestation
- Message encryption
- Public and private key attestation
- Cryptographic key management
- Ecosystem control, accessory authentication
- Disposable authentication
- Secure firmware update
- Key attestation
- Bus monitoring
If the TrustFLEX use cases do not meet the requirements of your authentication model, please look at our TrustCUSTOM platform.
Ready to Start Development?
To prototype security use cases with development kits, use the tutorials and code examples within the Trust Platform Design Suite (TPDS) software, which is available for Windows® and macOS® operating systems.
When working on custom configurations through TrustFLEX and TrustCUSTOM, request verification units by submitting the secure exchange questionnaire from TPDS and ordering verification units through microchipDIRECT.

Secure Exchange Process for TrustFLEX and TrustCUSTOM Devices
When using a TrustFLEX or TrustCUSTOM device customers need to securely transfer their key configurations to Microchip so the configurations and keys can be provisioned into verification units to determine if the configuration will go to production. In this video tutorial we walk through each step needed to properly fill out the secure exchange questionnaire, create a support case, download an encrypted provisioning package, order verification units and finally approve the design to go to production.
Tools and Software
- Demo & Evaluation Boards
- Development Environment
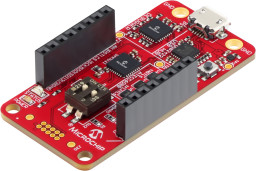
The CryptoAuth Trust Platform provides a compact development solution for developing IoT solutions with the ATECC608B-TNGTLS and ATECC608B-TFLXTLS and ATECC608B-MAHDA devices or the ATECC608C equivalents.
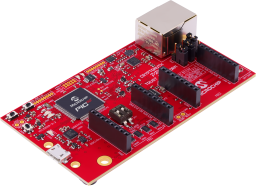
The Microchip CryptoAuth Pro Trust Platform is an enhanced version of the CryptoAuth Trust Platform Board containing and has a Arm® Cortex®-M4F Microcontroller, four on-board CryptoAuthentication devices, two mikroBUS™ sockets, and an on-board 10/100 Mbit Ethernet phy. Programming can be done via the on-board PKoB4 debugger which is compatible with MPLAB®X IDE. The board has been developed to work with Microchip's Trust Platform Development Suite of tools.
The Trust Platform Design Suite (TPDS) is our onboarding tool for our security-related solutions. The full onboarding experience includes, but is not limited to:
- Training and education about security concepts
- Prototyping, including dummy key generation and code examples, available via our interactive application notes
- Access to our provisioning system through a secure sub-system configurator and secure exchange process

MPLAB X IDE is a highly configurable software platform that provides powerful, free tools for developing, debugging and qualifying embedded designs that use microcontrollers and digital signal controllers.