CryptoAuthentication™ Family
What Is the CryptoAuthentication Family?
Featured Products
ATECC608
- Cloud IoT, firmware validation, secure boot assist, accessory authentication, IP protection and message encryption
- Supports asymmetric and symmetric key authentication with encryption
ECC204
- Accessory authentication, firmware IP protection, and disposable applications
- Cost-effective asymmetric/symmetric authentication with secure data storage; available in three-pin parasitic power and standard packages
ECC206
- Disposable and accessory authentication with firmware IP protection
- Compact two-pin parasitic power package; supports asymmetric/symmetric authentication and secure data storage
SHA105
- Host-side key protection for accessory and disposable authentication and firmware IP protection
- Pairs with SHA104/SHA106 for symmetric authentication and secure data storage
SHA104
- Client-side key protection for accessory and disposable authentication and firmware IP protection
- Pairs with SHA105; available in three-pin parasitic power and standard packages
SHA106
- Cartridge authentication for consumables in consumer, cosmetic, industrial, and medical applications
- 2-pin parasitic power package; pairs with SHA105 for symmetric authentication and secure data storage
TA101
- Supports the most complex automotive security use cases and offers the greatest key strength diversity of all secure ICs
- Enables patch updates, secure boot, TLS, HDCP, USB-C®, WPC Qi® 1.3 authentication and key management
TA100
- Covers common to complex automotive security needs
- Supports secure boot, TLS, HDCP, USB-C, WPC Qi 1.3 authentication and key management
TA101 TrustMANAGER and TrustFLEX Early Adopter Program
Get early access to TA101‑TFLX (TrustFLEX) and TA101‑TMNG (TrustMANAGER) beta silicon devices.
TA101‑TFLX is a robust secure key storage device paired with a set of predefined security protocols for teams who want to integrate TA101 into their own public key infrastructure (PKI) systems.
TA101‑TMNG includes the same key storage and protocol capabilities, but adds the keySTREAM cloud platform for remote configuration, PKI creation, key management, and firmware updates —removing the burden of building a managed IoT security infrastructure in‑house.

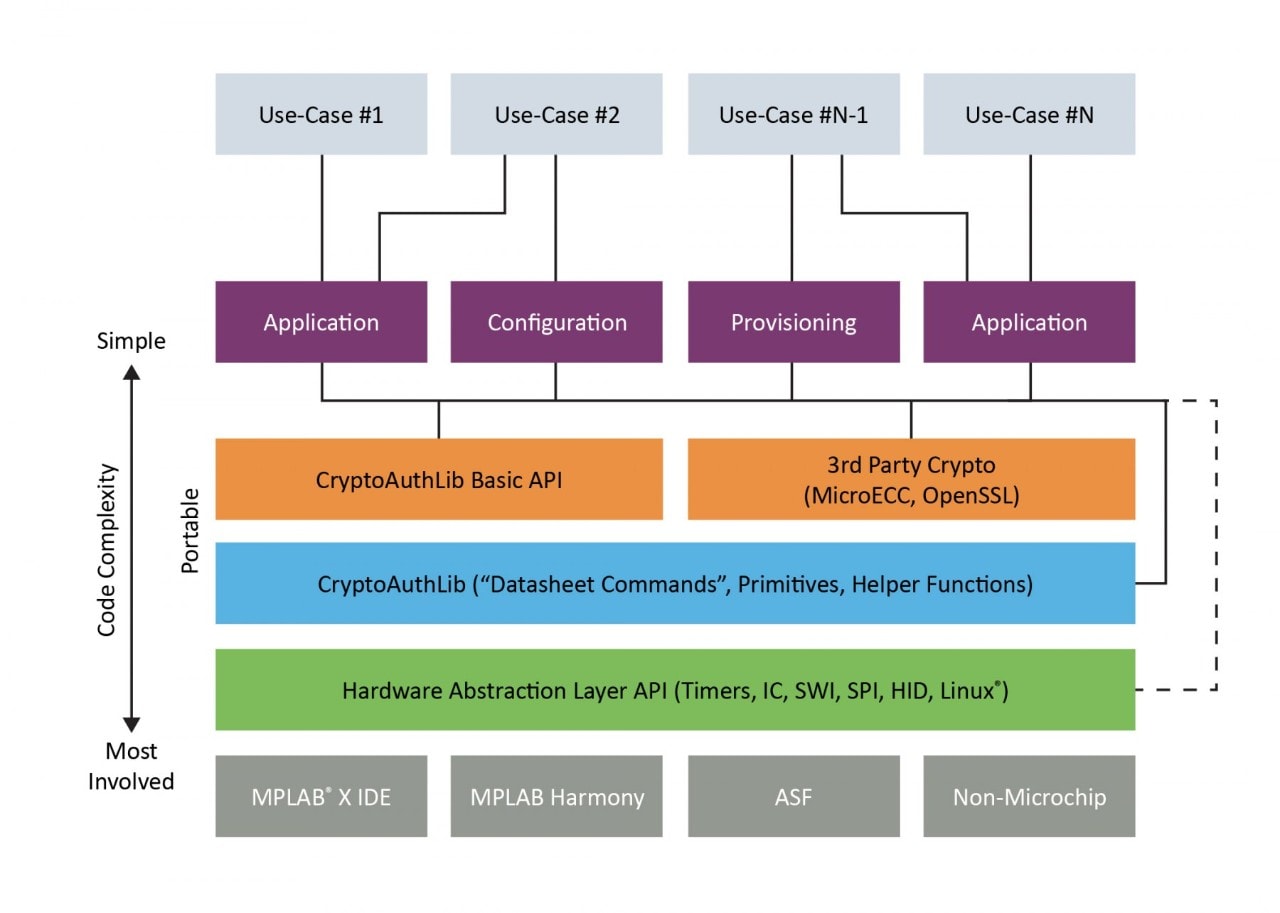
CryptoAuthLib Library
To streamline your development process with CryptoAuthentication devices like the ATECC608, ATSHA204A, ECC204, ECC206, SHA104, SHA105, SHA106, TA010 (automotive qualified) or ATSHA206A, we offer the CryptoAuthLib library. This software support library, written in C code, is essential for integrating cryptographic services into any application or device driver. It is compatible with a range of platforms, including Arm® Cortex®-M-based microcontrollers, PIC® microcontrollers and PCs that run Windows® or embedded Linux®.
Key Attributes
- Easy to use: Basic Application Programming Interface (API) serves the needs of most applications
- Powerful: Core API makes the full power of the device available for sophisticated applications and developers
- Portable: Runs on small processors and desktop systems
- Extensible: Designed to easily support new microcontroller platforms or protocols
- Flexible: Includes APIs for storing, retrieving and manipulating X.509 certificates and for Transport Layer Security (TLS) integration
If you need assistance during your design and development process, visit our technical support portal to find helpful resources and get assistance from our security experts. Our approved security design partners also offer expertise with TLS stack providers, cloud platforms, certificate authority companies and the CryptoAuthLib library to help you quickly and cost effectively bring your product to market.
Applications

IoT Authentication
Our CryptoAuthentication ICs provide secure hardware key storage to support encryption, decryption, and sign‑verify operations, enabling strong, scalable protection for IoT nodes across a wide range of applications.

Accessory Authentication
Our CryptoAuthenticaion ICs can be used to implement a controlled accessory ecosystem strategy, a third-party certification program or accessory counterfeit prevention.
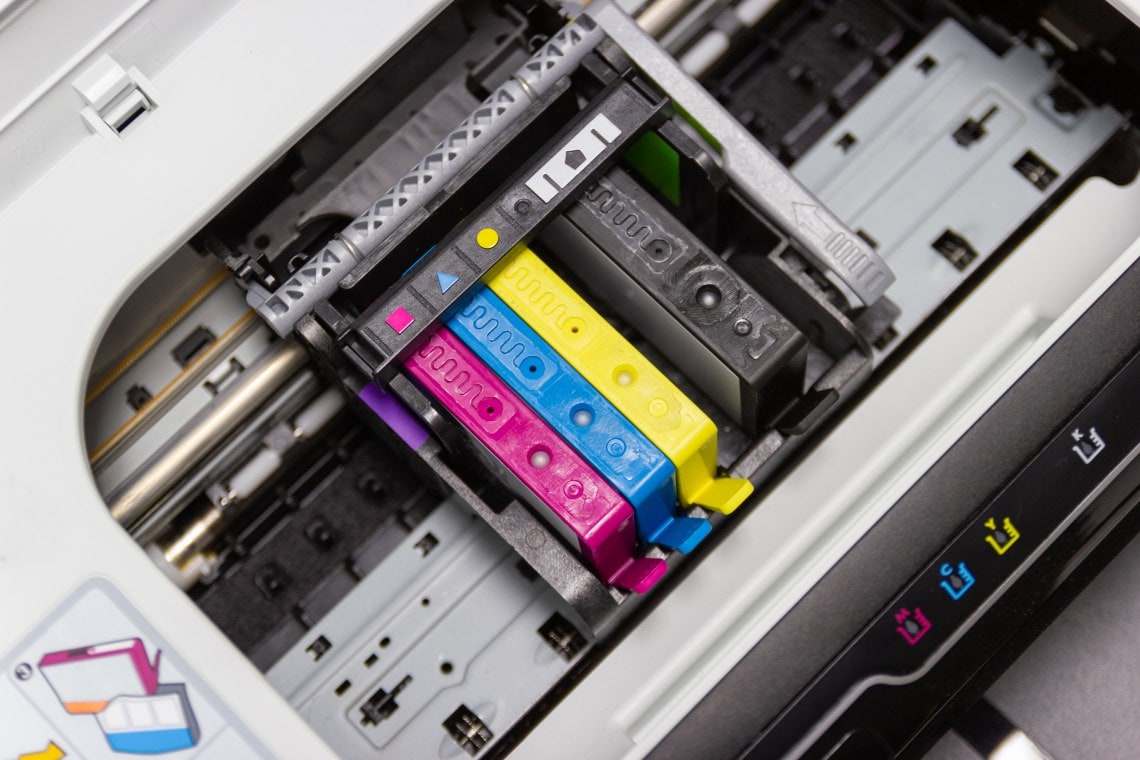
Disposable Authentication
Depending on the threat model your company identifies, you can leverage our CryptoAuthentication ICs to implement several secure authentication architectures to defend your single-use products from counterfeiting.
Trust Platform Provisioning Service
Use the Trust Platform Provisioning Service with four unique tiers of customer support and certified secure factories to leverage our pre-configured and pre-provisioned secure ICs with the most common security use cases.
The Trust Platform Design Suite (TPDS) tool includes secure IC configurators and use cases supported by code examples and tutorials to accelerate your development.
