Military-Grade Security by Design™
Trusted Hardware. Design Security. Data Security.
In defense, aerospace, industrial automation, Al/ML and critical infrastructure, compromise is not an option. Our PolarFire® FPGAs and SoCs offer proven, multilayered security. Starting with supply chain assurance that establishes hardware trust anchors, our tamper-resistance and secure boot secures the hardware and user design, and cryptographic engines secure the input and output data. Whether you're deploying Linux® at the edge or operating a satellite, PolarFire FPGAs and SoC FPGAs deliver the most secure platform in that class.
Comprehensive Security Architecture
- Trusted Hardware
- Design Security
- Data Security
- Embedded Security
- Secure Programming
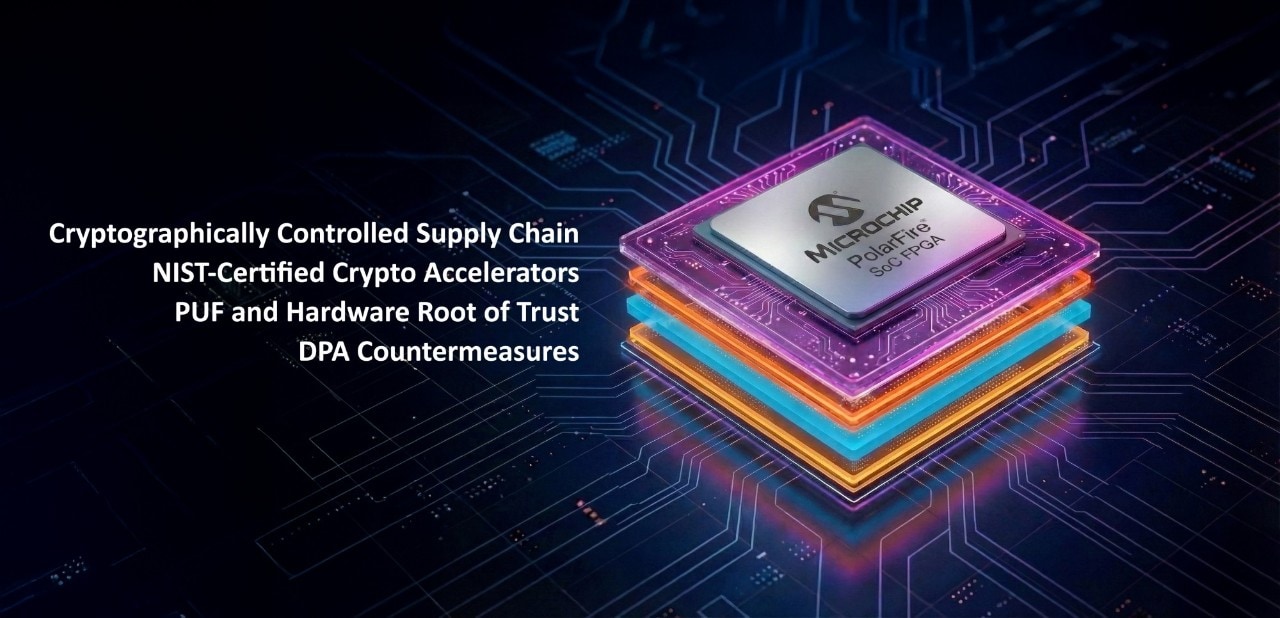
Security begins with hardware. PolarFire FPGAs and SoC FPGAs deliver military-grade protection, from design through field deployment and end-of-life, featuring:
- Cryptographically controlled supply chain:
- Cryptographic authentication at every step during the manufacturing flow prevents cloning and enables authentic products get built and delivered
- Device Integrity Value (DIV): You can verify the authenticity of the device procured and through the lifecycle of your system
- NIST-certified crypto accelerators:
- NIST Cryptographic Algorithm Validation Program (CAVP)-certified algorithms provide compliance to standards, which enables interoperability and robust security
- Hardened crypto engines provide deterministic performance and lifelong reliability
- PUF and hardware root of trust:
- Physically Unclonable Function (PUF) generates unique device-specific keys establishing a hardware root of trust for key storage and secure boot
- DPA countermeasures:
- Side-channel attack resistance with Rambus’ patent-protected Differential Power Analysis (DPA) countermeasure portfolio; Cryptography Research, Inc. (CRI) pass-through license that enables you to implement side-channel-resistant solutions
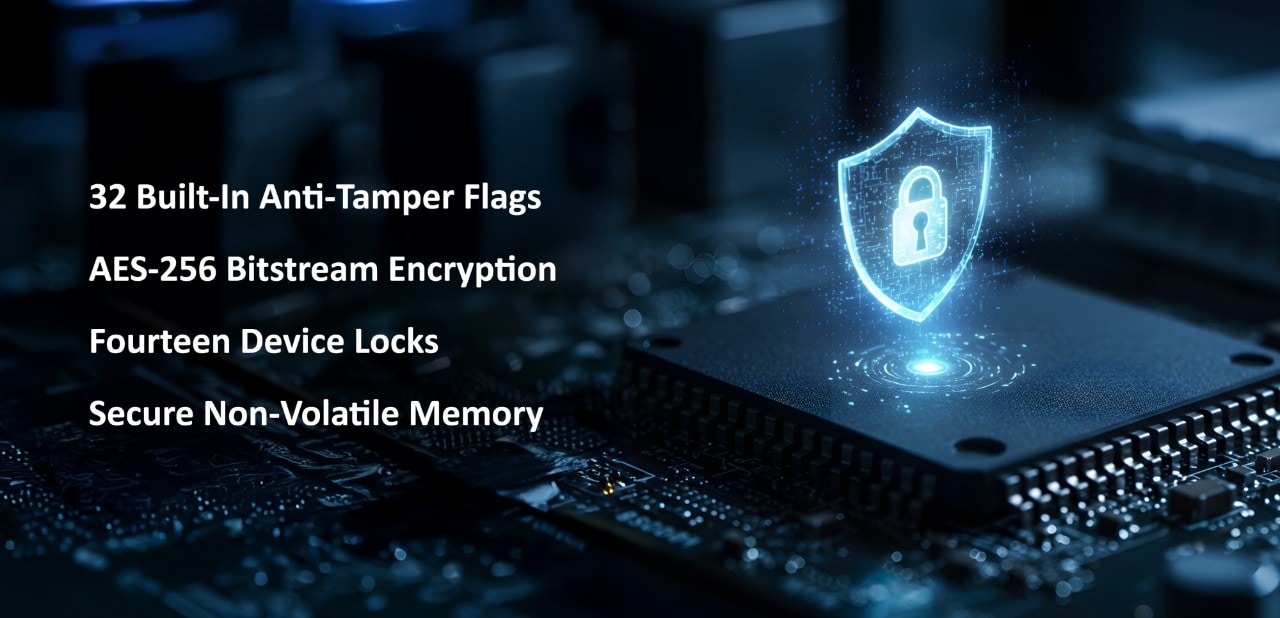
Our design security allows FPGA designs to operate as intended for the life of the product, while protecting intellectual property against theft, cloning or tampering.
Key Features
- 32 built-in anti-tamper flags
- Monitor voltage, temperature, clock frequency and clock anomalies
- Active tamper mesh detects probing and invasive attacks
- JTAG security monitor prevents unauthorized debug access
- User-selectable tamper response mechanisms, including zeroization of keys and entire design
- Bitstream security
- AES-256 Bitstream Encryption and Secure Hash Algorithm (SHA)-based authentication guarantee that only trusted designs can be loaded
- On-chip Nonvolatile Memory (NVM) confirms no external bitstream and no opportunity for interception
- 14 device locks
- Prevent overwriting user keys or security segments
- Disable debug features (SmartDebug, boundary scan, sensor readout, custom JTAG)
- Permanently disable factory test modes with passcode
- Use permanent locks to create an OTP/ASIC-like device
- Disable JTAG/SPI programming and in-application programming
- Lock FPGA or sNVM updates (override only with FlashLock passcode)
- Secure NVM
- Up to 56 KB of secure NVM
- Pages can be encrypted with PUF-derived keys
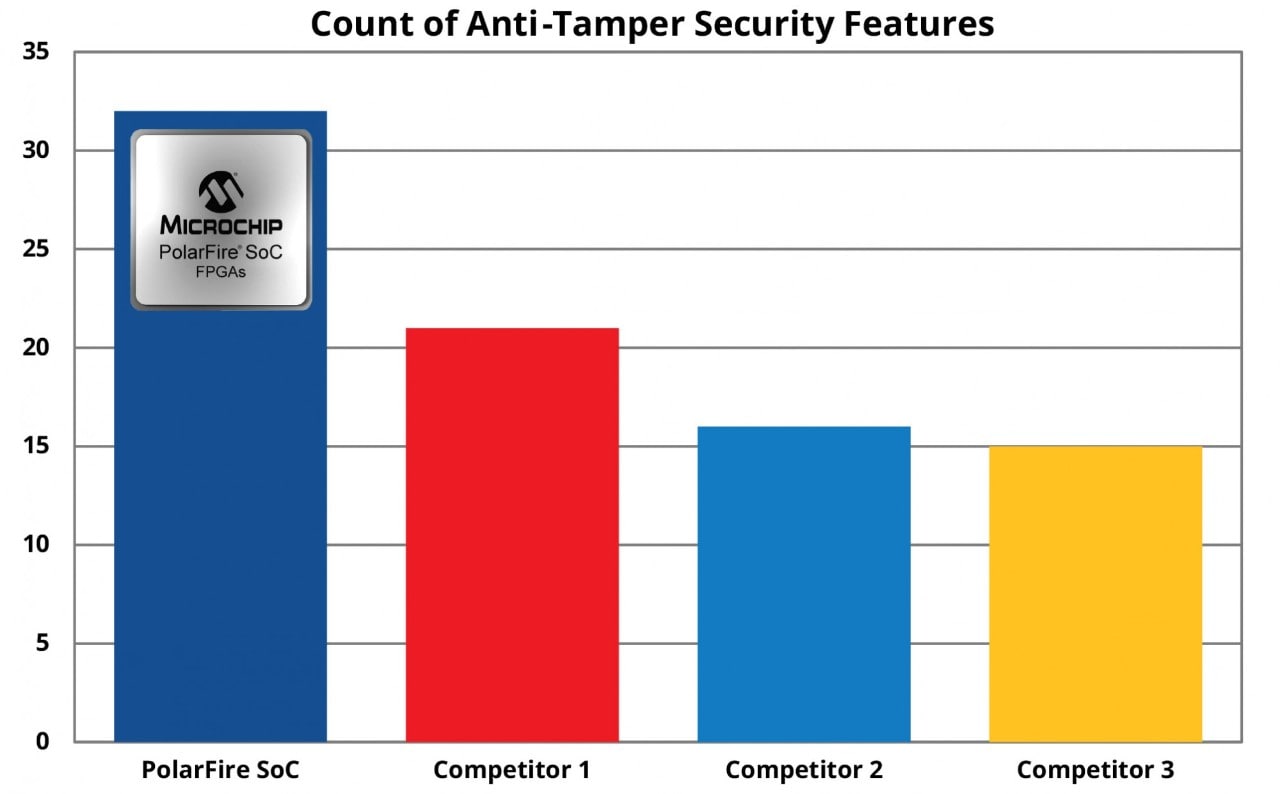
PolarFire FPGAs and SoC FPGAs Lead in Anti-Tamper Features
PolarFire FPGAs and SoC FPGAs include a number of built-in tamper detection and response capabilities that can be used to enhance the security of the device. These countermeasures are intended to address various types of attacks that include non-invasive, semi-invasive, and invasive attacks. The devices can detect a number of conditions that may indicate an attempt to tamper.

PolarFire FPGA and SoC FPGA data security features extend protection beyond configuration and IP, securing application data in motion and at rest.
Key Features
- Crypto co-processor (Athena F5200B): Hardened co-processor for Rivest-Shamir-Adleman (RSA), Elliptic Curve Cryptography (ECC), Advanced Encryption Standard (AES), Secure Hash Algorithm (SHA), and Hash-based Message Authentication Code (HMAC) techniques
- Offload crypto functionality to co-processor for DPA resistance, CAVP-certified algorithms, power- and cost-efficient cryptography
- Random number generator: Integrated TRNG enables secure cryptographic operations
- PUF-protected key storage: Keys derived uniquely per device, never exposed externally
PolarFire SoC FPGAs extend hardware trust into the software domain. Built on the industry’s first RISC-V®-based SoC FPGA platform, our embedded security establishes root of trust for embedded systems.
Key Features
- Secure boot, rooted in hardware
- Boot chain anchored in immutable Flash and PUF-derived keys
- Firmware payloads—bootloader, operating system and application—are authenticated before execution
- Prevents unauthorized or malicious code from execution
- Physical Memory Protection (PMP) and Memory Protection Unit (MPU)
- PMP (in the RISC-V cores) and MPU (in the Microprocessor Subsystem (MSS) enforce access rules in hardware and software
- Enable secure partitioning between trusted and non-trusted software
- Support mixed-critical systems where real-time control and open-source Linux® applications run side by side without loss of determinism
- Secure crypto partitioning
- Hardware crypto engines can be allocated exclusively to trusted domains
- Shared-MSS and fabric crypto modes give developers flexibility in assigning cryptographic workloads to different trust levels
- Runtime tamper response
- Integrated with hardware monitors: if tamper is detected, subsystems can trigger zeroization, lockdown or safe reset
Benefits
- Assured software authenticity: Applications only run if verified by the hardware root of trust
- Partitioned security: Developers can isolate sensitive control functions from higher level Linux workloads
- Defense against runtime attacks: Memory protection and tamper responses prevent privilege escalation and key leakage
PolarFire SoC Embedded Security
Learn more about PolarFire SoC FPGA embedded security with these Shields Up! webinars:
- PolarFire SoC FPGA Secure Boot
- Enabling Device Security with a Formally Verified Microkernel
- RISC-V Enclaves - A Clean Slate Approach to Linux Security
- Implementing Multizone Security In RISC-V Applications

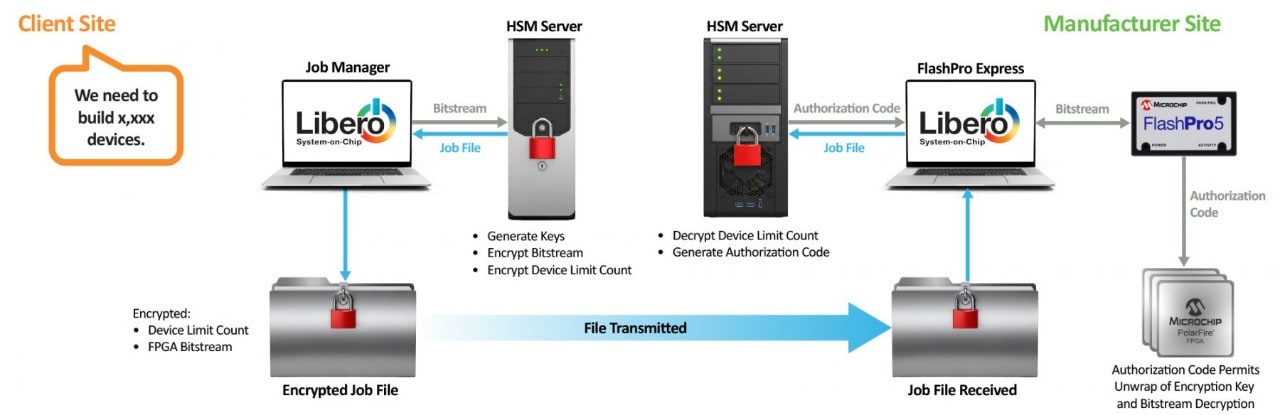
Our Secure Production Programming Solution (SPPS) enables you to deploy cryptographic control to your production flow at the:
Design Site (key functions):
- Define the programming request (e.g., 5,000 devices).
- Libero® SoC Design Suite Job Manager generates the bitstream.
- Hardware Security Module (HSM) generates keys, encrypts the bitstream, and sets device count—an encrypted job file is returned.
Manufacturing Site (key functions):
- Contract manufacturers load the encrypted job file into the system
- HSM decrypts the file, checks device limits and generates an authorization code
- Authorization code is passed back to programming tools
- Libero SoC Design Suite Job Manager/FlashPro Express unwraps the encryption key
- Bitstream is decrypted and programmed securely
Benefits of SPPS
- Separation of roles: Designers retain key control; manufacturers never see them
- Device count enforcement: Stops overbuilding and cloning
- HSM-based security: Keys generated and handled only inside a certified security modules
- Auditability: Certificates of compliance provide lifecycle traceability