Connect and Protect Your Embedded Applications
We provide solutions for creating smart, connected and secure IoT designs. This complete product offering simplifies the development of innovative systems which reduces your time to revenue.
Through our ready-to-use tools, partnerships with major cloud computing companies and world-class support, our comprehensive design resources make your journey from idea to cloud fast and easy.

Smart, Connected and Secure

Smart
Add intelligence to your IoT design with our vast selection of digital, analog and mixed-signal products that help with sensor node signal conditioning, edge computing, power management and other requirements.

Connected
Connect your IoT design quickly and easily with our wired and wireless devices that are designed to be compatible with our MCUs, MPUs, and other devices.

Secure
Find the security implementations that meet your unique needs with our wide range of hardware- and software-based solutions for applications ranging from secure authentication to trusted execution environments and more.
Learn More About Designing IoT Devices for Your Market
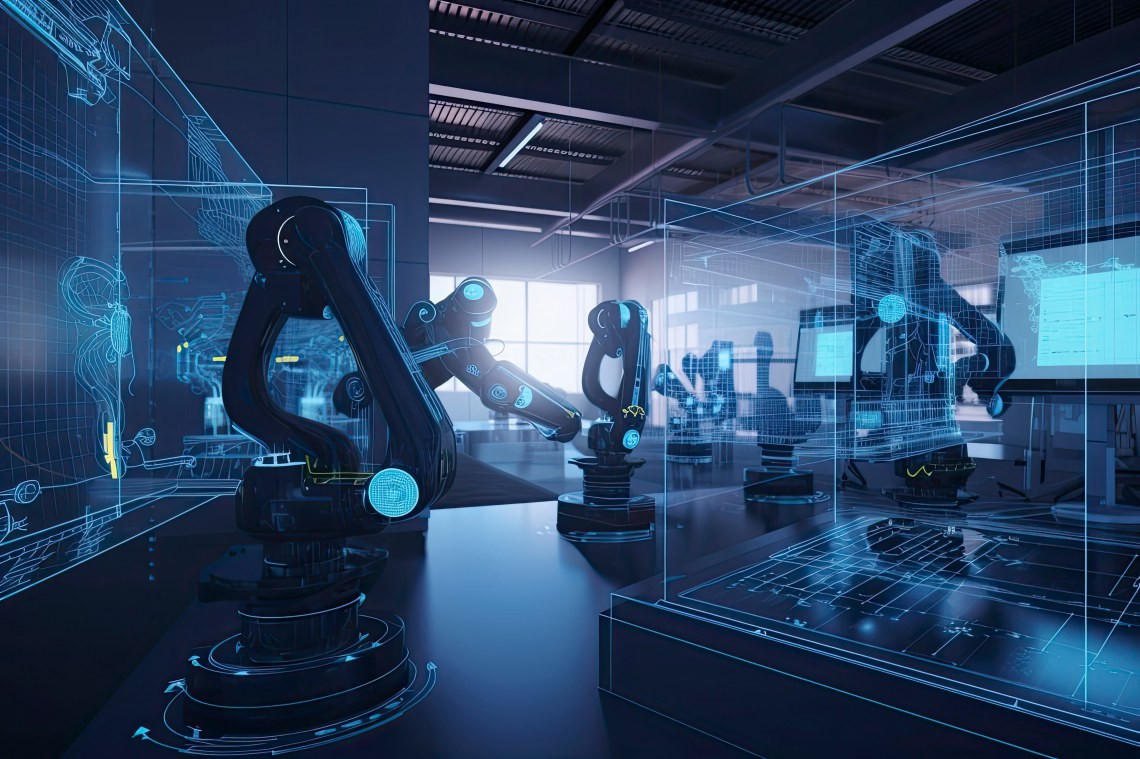
Smart Factory
Optimize equipment health, ensure worker safety and enhance business profits.

Smart Medical
Develop telehealth, connected drug delivery and connected clinical devices.

Smart Building
Discover how our advanced technologies, solutions and services can transform your building's operations.

Smart Agriculture
Optimize resources and enhance crop quality to improve security and profitability.

Smart Construction and Mining
Our industry-tested technology provides long service life, adaptive and autonomous control, and efficient operations with a focus on sustainability.
Securely Connect Your Devices To Our Cloud Partners



Microchip University Online Learning

Create a Managed IoT Device Leveraging Microsoft Azure IoT

Controlling Your IoT Device Using Amazon Alexa

Provision IoT Devices From Prototype to Production

View All Online Microchip University IoT Courses
Additional Resources

Contact Our Client Support Team
We are here to support you. Live chat, email, or schedule a call with our Client Support Team to get assistance with device selection, project review, project redesign and more.

Professional Design Services
Need help with your IoT design? Our Cloud, Wireless, and App Developer Design Partners can help connect your device to the internet and accelerate your time to market.

Information and Resources
Browse through our featured IoT content including articles, technical videos, webinars and innovative new products.