AWS Greengrass
Simplifying Development with Our Comprehensive Kit
AWS Greengrass Hardware Security Interface (HSI)
Our Linux Offerings Simplify Your Software Implementation
Simplify Your Gateway Design by Using a SiP or SOM
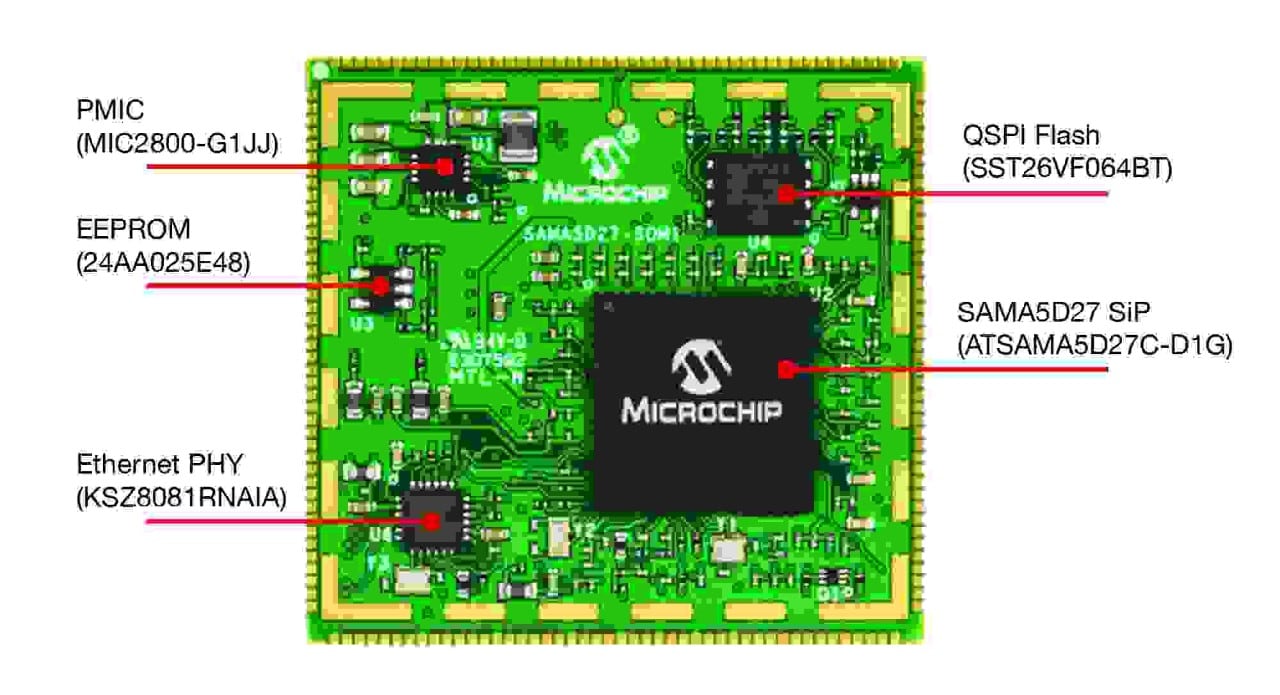
Our System On Module (SOM) and System in Package (SiP) options ease the design of a microprocessor (MPU)-based system and can be used for industrial-grade designs. They ensure signal integrity for the high-speed interfaces to DDR memory and, in the case of the SOM, the Ethernet Physical layer (PHY) while complying with Electromagnetic Compatibility (EMC) standards. You can solder the SOM on a motherboard and take it to production or use it as a reference design for your custom hardware, along with the free schematics, Gerber files and complete bill of materials, all available online. Our Linux development code will immediately run on the SOM, allowing you to get to production release even faster.
Secure Elements Empowered by Greengrass HSI
Before a connection between a host and a client is completed, trust must be established based on a unique, trusted, protected identity. This identity is the private key that will be used to authenticate a cloud service, a gateway or an edge node. Security is only as strong as its weakest link and too often private keys are left accessible in processors memories. An attacker can easily obtain the key, even if it’s encrypted, and impersonate the Linux-based system. To address the issue, AWS Greengrass offers a feature called Greengrass HSI that is an interface to communicate between the Greengrass core and a secure element, like the ATECC608B, using the PKCS#S11 library. With its JIL “high“ rated security grade, the ATECC608B empowered by Greengrass HSI brings the capability to add hardware-based secure key storage to any Linux system. All the cryptographic functions involved with keys remain inside the secure boundaries of the ATECC608B where the private key is generated, stored and protected. Greengrass HSI sends a challenge to the secure element which will answer with a response containing a signature based on the stored private key. The authentication, one of the security pillars, relies now on an adequately protected root of trust. The ATECC608B is also part of the AWS Device Qualification Program supporting AWS Greengrass.
Development Tools

Secure 4 click
The Secure 4 click from MikroElektronika features an ATECC608 and a Raspberry Pi® adapter. It can be used with any Greengrass-enabled Raspberry Pi hardware to leverage the Greegrass HSI on your Linux-based system. The ATECC608 secure element is a JIL "High" rated secure key storage device equipped with side attack channel and active anti-tamper protections to isolate keys and other secrets from being exposed during authentication between Greengrass and AWS IoT.

SAMA5D27-SOM1-EK1
Part Number: ATSAMA5D27-SOM1-EK1
The ATSAMA5D27-SOM1-EK1 is a fast prototyping and evaluation platform for the SAMA5D227C-D1G System in Package (SiP). Use this kit with the Linux distribution and software packages to jump-start the development of your IoT projects.
Third-Party Tools
ZYMKEY 4i
The ZYMKEY 4i is an IoT security module for use with a Raspberry Pi® and AWS Greengrass. This add-on solution features an Arm® Cortex®-M0+ based SAM D21 MCU as the interface between the Linux machine and the secure element where the keys and other credentials are protected.

Products
- SAMA5 Products
- Secure Element for Public Clouds Product