Leverage the Simplicity of Generic Certificate Authentication
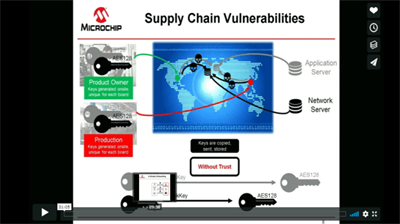
When it comes to IoT security, authentication is one of the foundational concepts that should be implemented first in your design. The trust between the device identity and the cloud platform relies on a chain of trust. AWS IoT Core supports generic certificate-based authentication, but the trust in the device identity will depend entirely on how well the device’s private key is protected. If the private key is spoofed, the device can be impersonated by an unauthorized user who can then control the device’s transactions. However, adding authentication presents you with several challenges: securely storing the private key in the device, shipping the private key across the globe for any project and system size, creating a possibly cost-prohibitive chain of trust and ensuring a secure manufacturing flow. These challenges can be addressed by using the Trust&GO ATECC608B-TNGTLS secure element from our Trust Platform family of solutions on AWS IoT Core.

To prototype with the proposed development kits, use the tutorials and code examples within the Trust Platform Design Suite software available for Windows® and macOS® operating systems.
When you are ready to go to production, order the pre-provisioned devices and download the manifest file from Microchip Direct or from our distribution partners. Upload the list of public credentials in the corresponding cloud account.

Benefits of Using the Trust&GO ATECC608B with AWS IoT Core
- Pre-configured device and pre-provisioned private key
- Create secure authentication to IoT devices powered by AWS IoT Core
- Benefit from the scalability of AWS IoT Multi-Account Registration
- Leverage the simplicity of generic certificate authentication
- Implement a unique, trusted, protected and managed device identity
- Turnkey code examples available for 32-bit microcontrollers
- Leverage Microchip’s secure provisioning service
- Simplify logistics of shipping private keys and reduce manufacturing costs
- Microcontroller-agnostic implementation
- JIL rated “high” secure key storage
- Protection against known tamper, side-channel attacks
Trust&GO ATECC608B-TNGTLS Features
Each of the device slots are pre-configured and pre-provisioned to offer the following use cases:
- Generic Certificate Authentication: Use the default generic certificates for thumbprint authentication already locked inside the Trust&GO device; the cloud architecture will not need to use a root certificate to verify the thumbprint certificate, but the server will have to be set up to implement this policy.
- Token Authentication: Leverage a private key to perform an Elliptic Curve Digital Signature Algorithm (ECDSA) sign operation on a token that will be verified by its corresponding public key somewhere else in the network.
Visit the ATECC608B-TNGTLS product page to learn more about the device’s features.
Trust Platform Design Suite
Install the Trust Platform Design Suite software package to get started with any of the Trust&GO or TrustFLEX secure elements available with our Trust Platform. Our tutorial will guide you through the installation of the tools that will simplify your development from prototyping to production and accelerate your time to market.
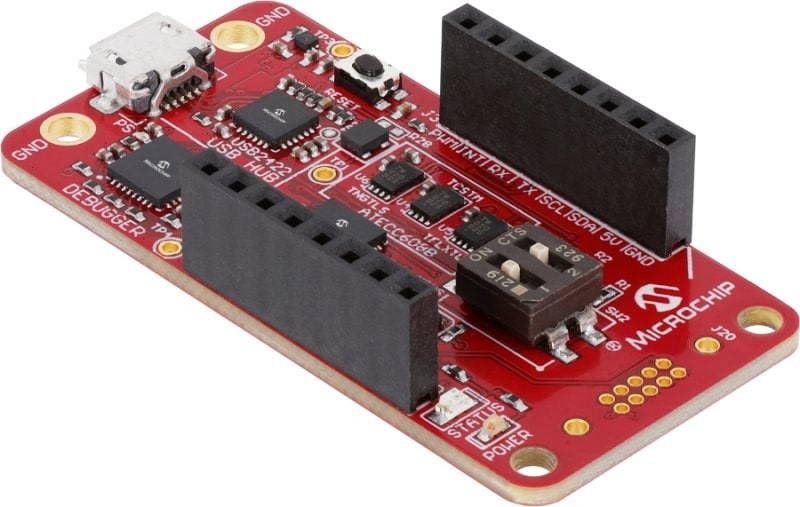
CryptoAuth Trust Platform Development Kit
Part Number: DM320118
This USB-based development kit includes a SAM D21 MCU, debugger, mikroBUS™ socket and on-board ATECC608B secure element with Trust&GO, TrustFLEX and TrustCUSTOM options.

ATECC608B Trust Platform Kit
Part Number: DT100104
For use as an add-on board to the CryptoAuth Trust Platform Development Kit (DM320118), this kit provides a mikroBUS footprint for adding soldered-down versions of Trust&GO, TrustFLEX or TrustCUSTOM secure elements.

CryptoAuthentication™ SOIC Socket Kit
Part Number: AT88CKSCKTSOIC-XPRO
This board provides an SOIC8 socket to accommodate an ATECC608B or ATSHA204A secure element and an Xplained Pro (XPro) interface to develop solutions using the microcontrollers featured on our Xplained Pro boards.

CryptoAuthentication UDFN Socket Kit
Part Number: AT88CKSCKTUDFN-XPRO
This board provides a uDFN8 socket to accommodate an ATECC608B or ATSHA204A secure element and an Xplained Pro (XPro) interface to develop solutions using the microcontrollers featured on our Xplained Pro boards.
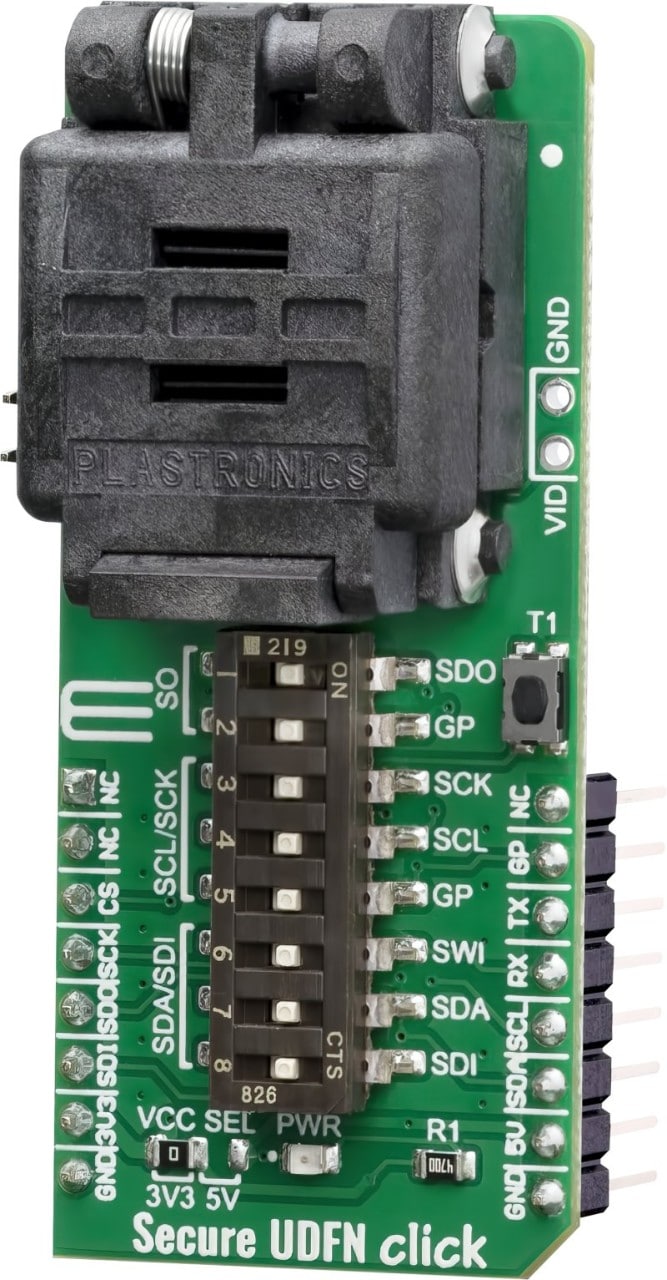
Secure UDFN click
This Click board™ from MikroElektronika provides a uDFN8 socket to accommodate an ATECC608B or ATSHA204A secure element and operate it on the CryptoAuth Trust Platform Development Kit (DM320118).

WiFi 7 click
This Click board™ from MikroElektronika includes an ATWINC1500 Wi-Fi® module which can be used to add TCP/IP and TLS links to the CryptoAuth Trust Platform Development Kit (DM320118).

Shuttle click
This Click board™ from MikroElektronika provides an easy and elegant solution for stacking up to four Click boards on a single mikroBUS™ socket.

mikroBUS Shuttle
This small add-on board is intended to be used with Shuttle click to expand the mikroBUS™ socket with additional stacking options. One Shuttle click can support up to four mikroBUS Shuttles, allowing a simple and elegant stacking solution for the Click board™ line of products.
- Documents
- Videos
- FAQ
- Definitions
- Archives
- Microchip University

AWS IoT Security: The New Frontiers
In this session from AWS re:Invent 2016, AWS explains the value of Just in Time Registration (JITR) and Bring you Own Certificate (BYOC) using an ATECC508A secure element.
AWS re:Invent 2016: Introduction to AWS IoT in the Cloud
In this session from AWS re:Invent 2016, an AWS IoT product manager discusses why protecting a devices identity is important and how it can be implemented using the ATECC508A secure element with the AWS IoT service.

Hardware Root of Trust with Google Cloud IoT Core and Microchip
Check out how to improve IoT security by securing the authentication between Google Cloud IoT Core and IoT devices using an ATECC608B secure element.

Internet of Things (IoT) Security Best Practices With Google Cloud (Cloud Next '19)
Security is a critical concern when deploying and managing IoT devices. Learn how Cloud IoT provisioning service simplifies the device provisioning and on-boarding experience for Cloud IoT customers and OEMs. We will demonstrate how to efficiently do bulk provisioning of 8-, 16- and 32-bit microcontrollers. You will also learn about best practices and practical examples of how to provision devices in the wild and keep them secure for their lifetime.

IoT Security: Solving the Primary Hurdle to IoT Deployments (Cloud Next '18)
Security is a huge hurdle to IoT deployment. No company wants to be in the news for having its product as part of a large, IoT-driven DDoS attack. In this session you will learn how Google and Microchip have partnered to offer a seamless and highly secure solution for IoT devices connecting to Google Cloud IoT.

Secure Authentication for LoRa® with the ATECC608B and The Things Industries (TTI) Join Server
In this archived Livestream event, our security experts discuss how to easily develop a LoRa-connected device with secure authentication using our robust, yet simple-to-use, hardware-based security solution using our ATECC608B secure element, SAM R34 radio and The Things Industries (TTI) join server.

Secure Provisioning Service with the Trust Platform for the CryptoAuthentication™ Device Family
In this episode of the Microchip SHIELDS UP! series of security webinars, we provide an overview of the Trust Platform service for the CryptoAuthentication™ family of devices. You will learn about the pre-provisioned Trust&GO, pre-configured TrustFLEX and fully customizable TrustCUSTOM options for the ATECC608B. You will also be given a high-level description of the on-boarding process and the basic information you need to get started with using the provisioning services available from our factories.
Secure Download Firmware Update (DFU)
Learn how to implement a secure, Over-the-Air (OTA) firmware update with a traditional microcontroller using a Microchip secure element such as the ATECC608B. This simple-to-use, cost-efficient and robust security implementation protects the key by verifying the signed code comes from a legitimate source. The key remains protected by leveraging the ATECC608B secure element. Both asymmetric and symmetric architectures are covered in the video.

AWS IoT Authentication Use Case
Microchip explains how hardware root of trust works using the ATECC608B secure element and AWS IoT. The Just In Time Registration and Use Your Own certificates functions from AWS IoT allow large-scale authentication of automated systems, while maintaining security by protecting private keys from users, software and manufacturing backdoors.

Cryptography Primer (Part 1): Why Security Today?
During this tutorial about embedded security, Microchip discusses why security is an important consideration.
Cryptography Primer (Part 2): Authenticity, Integrity and Confidentiality
During this tutorial about embedded security, Microchip discusses the three key pillars of security: authentication, integrity and confidentiality.
Cryptography Primer (Part 3): Hashing, Secret Key and Symmetric Cryptography
In this video, learn about the basics of embedded security and how and when to use hashing.
Cryptography Primer (Part 4): Public Key and Asymmetric Authentication
During this tutorial about embedded security, Microchip discusses the concepts of asymmetric cryptography, illustrates how authentication can be implemented and highlights the importance of protecting private keys in hardware secure key storage.

Cryptography Primer (Part 5): Chain of Trust
In this cryptography primer tutorial, Microchip discusses how to implement robust authentication between a host and a client using Public Key Infrastructure (PKI).

Google Cloud IoT Core Authentication Use Case
Check out how Google Cloud IoT combined with the ATECC608B secure element strengthens device-to-cloud authentication. This flexible and TLS-agnostic implementation leverages the JWT token and optimizes code size to enable connectivity and security for very small microcontrollers.
Hardware Root of Trust for AWS IoT with ATECC608B
The threat model for IoT devices is very different from the threat model for cloud applications. During this session at AWS re:Invent, we discussed how all IoT solutions must incorporate end-to-end security from the start, how to mitigate threats and how to avoid common pitfalls. You will also learn about the steps to take in the manufacturing process, how to provision and authenticate devices in the field and how to comply with IT requirements during the maintenance phase of the product lifecycle.
How to Build a Secure Provision Workflow - The Things Conference 2019
Manipulating application and network server keys is not only a daunting process but also opens backdoors in LoRaWAN™ connected products. In this workshop recorded at The Things Conference 2019, you’ll find out how to use Microchip’s secure element to build a secure provision workflow and strengthen authentication to The Things Industry’s (TTI’s) join server.

Secure Boot for Small Microcontrollers
Learn how to implement a secure boot architecture on very small microcontrollers using the ATECC608B secure element. Keys are protected from users, factory operators and equipment as well as software.
Secure Boot with ATECC608B
Learn how to architect a secure boot with Microchip's ATECC608B secure element. This solution implements strong security by verifying the signed boot image of a small microcontroller with an immutable public key kept in the secure element.
General Questions:
Q: How can I get started with the Trust Platform?
A: Use the “Let Us Guide You to the Right Option” on the Trust Platform page, which will help you take the first step. You will find additional information about getting started with Trust&GO, TrustFLEX and TrustCUSTOM on their pages.
Q: I am a distribution partner. How do I enroll in the Trust Platform program?
A: Contact your local Microchip sales office to request assistance with joining the program.
Trust&GO Questions:
Q: Do I need to contact Microchip to provision my Trust&GO secure element?
A: No. When you buy the device, it is already provisioned with keys and certificates specific to the use case you have selected that are locked inside the device. Trust&GO cannot be altered and is intended to be used as is.
Q: Where can I obtain the public keys and certificates for my Trust&GO device?
A: Log into your customer account at the ecommerce website where you purchased the device after device shipment, and you should be able to download a manifest file containing all the necessary public keys and certificates. Contact the vendor if you have any trouble finding this file.
TrustFLEX Questions:
Q: Do I need to contact Microchip to provision my TrustFLEX secure elements?
A: Yes. When you buy the device, it comes pre-configured with your selected use case(s). By default, the TrustFLEX device also come with keys and generic certificates for thumbprint authentication that are overwritable internally if you have not already locked them using the lock bit. While the configuration cannot be altered, the default credentials can be changed if you have not already locked them. If you decide to use the default credentials, you will have to lock them after receiving the device. If you don’t want to use the default credentials, you can replace them with yours and then lock them. After you have made your decision, create the secret packet exchange, encrypt it and upload it into a support ticket on Microchip’s technical support portal. We will provision your devices and ship them according to your instructions.
Q: Where can I obtain the public keys and certificates for my TrustFLEX device when I use the default credentials?
A: Log into your customer account at the ecommerce website where you purchased the device after device shipment, and you should be able to download a manifest file containing all the necessary public keys and certificates. Contact the vendor if you have any trouble finding this file. WARNING: If you have overwritten the default credentials in your device, the manifest file will no longer be compatible with the device’s new credentials.
TrustCUSTOM Questions:
Q: Do I need to contact Microchip to provision my TrustCUSTOM secure element?
A: Yes. When you buy the device, it will be blank. You will need to use the TrustCUSTOM configurator, which is available under Non-Disclosure Agreement (NDA) to define the configuration, create the secret packet exchange, encrypt it and upload it into a support ticket on Microchip’s technical support portal. We will provision your devices and ship them according to your instructions.
Q: Where can I obtain the secret packet exchange for my TrustCUSTOM device?
A: This utility is only available through a Non-Disclosure Agreement (NDA). Contact your local Microchip sales office or distributor to request it.
Q: Where can I get the full data sheet for my TrustCUSTOM device?
A: This document is only available through a Non-Discloser Agreement (NDA). Contact your local Microchip sales office or distributor to request it.
Credentials: Identity verification tools or methods that include X.509 certificates, generic certificates for thumbprint authentication, keys and data packets
Customization: The action of creating a unique device/system through its configuration and set of secrets
Firmware Verification: When a key and cryptographic operation are used to verify a signed image on a device at boot up or during run time
IP Protection: When a key and a cryptographic operation are used to verify signed (or hashed) firmware that is considered Intellectual Property (IP) of a product
Key(s): A set of binary numbers that is used to trigger a cryptographic algorithm that implements asymmetric or symmetric encryption
Over-the-Air (OTA) Verification: When a key and a cryptographic operation are used to verify a signed image that has been loaded into a connected device by a push notification from a cloud service
PKI: Public Key Infrastructure
Provisioning: The action of generating a credential into an embedded storage area
Birth Certificate: An X.509 certificate not issued by a certificate authority company that is used for authentication to the cloud
AWS IoT Core Certificate-Based Secure Authentication with 32-bit Microcontroller and ATECC508A
AWS IoT Core Certificate-Based Secure Authentication with 32-bit Microcontroller and ATECC608A
LoRa®-Based Secure Authentication for The Things Industries
Secure Boot Verification Assistance Using Small Microcontrollers and ATECC608A