Trust&GO Platform
Pre-Configured and Pre-Provisioned Secure Elements for Cloud Authentication
Are you looking for a quick and easy way to implement secure authentication for your Internet of Things (IoT) design? Our Trust&GO platform is designed to streamline the process of enabling network authentication using our ATECC608C secure elements. With a Minimum Orderable Quantity (MOQ) of just ten units, this solution is a great option for the smallest projects up to large-scale deployments. All you need to do is buy the devices, claim them and you are ready to get started.
- If you are using TLS-based authentication, we offer devices with a pre-established locked configuration and pre-provisioned and locked generic certificate for thumbprint authentication and keys
- We also offer code examples for a selection of use cases to support your application development

What Are the Benefits of Using Trust&GO Devices?
- Significantly reduces your development time because the secure element configuration tasks are already done
- Eliminates the need to purchase an expensive certificate chain since the credentials are built into the Trust&GO device
- Leverages our provisioning infrastructure to automatically implement secure key storage without the risk of exposing your credentials during the manufacturing process or mismanaging them after deployment
- Provides complete code examples for a variety of popular use cases so you can focus on your application code
- Comes with a manifest file containing public certificates and keys corresponding to the private keys protected inside the device
- Offers a low MOQ for small-volume projects of as few as ten units
Ready to Get Started With Trust&GO?
To prototype with the development kit, use the tutorials and code examples within the Trust Platform Design Suite (TPDS) software, which is available for Windows® and macOS® operating systems.
When you are ready to go to production, order the pre-provisioned devices and download the manifest file from microchipDIRECT.

Tools and Software
- Demo & Evaluation Boards
- Development Environment
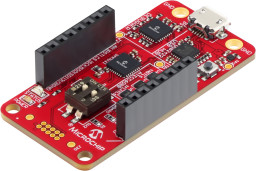
The CryptoAuth Trust Platform provides a compact development solution for developing IoT solutions with the ATECC608B-TNGTLS and ATECC608B-TFLXTLS and ATECC608B-MAHDA devices or the ATECC608C equivalents.
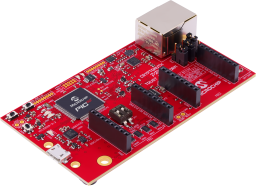
The Microchip CryptoAuth Pro Trust Platform is an enhanced version of the CryptoAuth Trust Platform Board containing and has a Arm® Cortex®-M4F Microcontroller, four on-board CryptoAuthentication devices, two mikroBUS™ sockets, and an on-board 10/100 Mbit Ethernet phy. Programming can be done via the on-board PKoB4 debugger which is compatible with MPLAB®X IDE. The board has been developed to work with Microchip's Trust Platform Development Suite of tools.
The Trust Platform Design Suite (TPDS) is our onboarding tool for our security-related solutions. The full onboarding experience includes, but is not limited to:
- Training and education about security concepts
- Prototyping, including dummy key generation and code examples, available via our interactive application notes
- Access to our provisioning system through a secure sub-system configurator and secure exchange process

MPLAB X IDE is a highly configurable software platform that provides powerful, free tools for developing, debugging and qualifying embedded designs that use microcontrollers and digital signal controllers.

