Security Mesh: Distributed Defense Across Your Design
Physical access changes the threat model. This post examines how invasive silicon attacks bypass software defenses and how our PolarFire® family and PolarFire SoC FPGAs counter them with an on-chip security mesh that detects tampering and enables immediate hardware-level response.
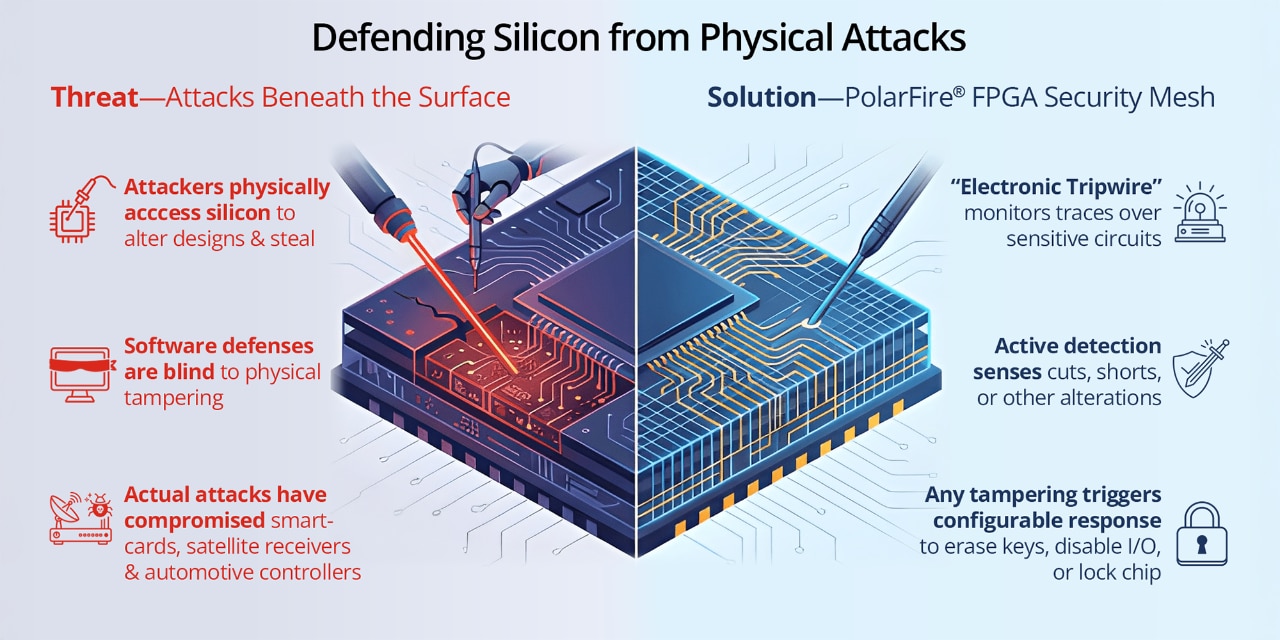
As software security mechanisms grow more sophisticated, they continue to rely on a critical assumption: that the underlying hardware is trusted and protected. This assumption does not always hold. Once an attacker gains physical access to a device, an entirely different class of threats emerges that traditional security systems cannot detect or prevent. In certain situations, adversaries possess substantial resources, such as advanced equipment and considerable financial backing, which is often characteristic of major organizations or nation-state actors. In these circumstances, physical security is an essential component of effective cybersecurity.
Adversaries or competitors may employ invasive methods—such as decapsulation, micro probing or laser fault injection—to directly access the underlying silicon. These techniques enable the extraction of confidential keys, reverse engineering of circuit designs or modification of configuration fuses, often undetectable by conventional software-based security measures.
Microchip’s PolarFire® family and PolarFire SoC FPGAs provide enhanced protection through the integration of a physical security mesh within silicon. In addition to cryptography and firmware safeguards, this security mesh actively monitors and responds to physical tampering attempts in real time.
The Problem: The Cost of a Breached Package
Physical intrusion is not merely hypothetical; it has been substantiated within the semiconductor industry over many decades.
Real-World Incidents
- Smartcard Decapsulation (2000s): Attackers successfully removed IC packaging and used micro probing to extract cryptographic keys from banking smartcards.
- Satellite Receiver Hacks (2010s): Reverse engineers used laser fault injection to alter configuration fuses and unlock protected firmware.
- IoT and Automotive ECUs (Recent): Researchers have shown how de-layering techniques and focused ion beams (FIBs) can access internal buses—bypassing security fuses or debug locks.
All these attacks needed physical access to silicon, making even strong encryption vulnerable.
The PolarFire Solution: Security Mesh
PolarFire family and PolarFire SoC FPGAs integrate a silicon‑level security mesh that provides hardware‑based protection against physical tampering. Implemented as a network of conductive traces over security‑critical circuitry, the system controller actively drives the mesh to establish baseline integrity. Any disruption caused by physical attacks—such as decapsulation, probing, grinding or energy‑based techniques—results in a tamper event.
The mesh spans sensitive regions of the device, including configuration memory and cryptographic key storage, providing protection where physical attacks are most impactful. When a tamper event occurs, it is detected at the hardware level and made available for a system‑level response.
Detection and Response
During normal operation, the system controller monitors the electrical characteristics of the mesh to detect loss of continuity. Upon detection, a tamper signal is asserted and routed to user‑defined logic in the FPGA fabric, allowing designers to implement application‑specific countermeasures. These may include zeroization of cryptographic keys, zeroization of secure non‑volatile memory (sNVM), disabling I/O interfaces, halting fabric operation, forcing a secure reset or placing the device into a locked or inoperable state.
Because detection occurs at the hardware level and response logic resides on‑chip, mitigation is immediate and does not rely on firmware execution—providing an effective defense against invasive physical attacks.
Use Case: Hardware Assurance in Defense Systems
FPGA-based systems are commonly used in defense scenarios where retrieving hardware after a mission isn't always feasible. Devices might be abandoned in hostile environments, potentially falling into the hands of adversaries or competitors equipped with resources for invasive analysis. If silicon-level protection is lacking, this access could reveal sensitive firmware, cryptographic keys or authentication methods.
By enabling the security mesh and configuring a tamper-response chain, designers can be confident that:
- Any physical intrusion attempt instantly erases critical data.
- The board remains inoperable until securely reprogrammed.
- System integrity is preserved, even under physical duress.
The Takeaway: Hardware Security is Central to Cybersecurity
Cybersecurity often focuses on code and data. When physical access to a device is possible, software‑only defenses are insufficient. Addressing this risk requires security mechanisms that operate below the software and firmware layers.
By integrating a security mesh directly into silicon, PolarFire family and PolarFire SoC FPGAs provide a foundational layer of physical protection that complements existing cryptographic and system‑level protections.