MiWi™ Software Vulnerability
The following issues affect version 6.5 of MiWi software.
Affected Products and Resolution
- Early Frame Counter Validation
- Validation of Only Two Out of Four MIC Bytes
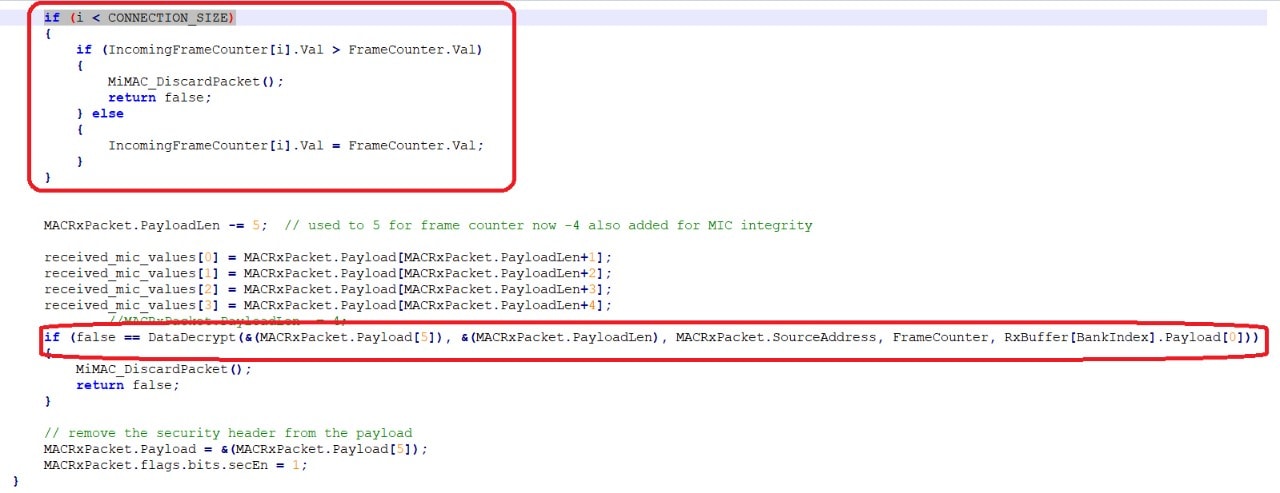
Early Frame Counter Validation
In version 6.5 of our MiWi software and all previous versions including legacy products, there is a possibility of frame counters being validated/updated prior to the message authentication. With this vulnerability in place, an attacker may increment the incoming frame counter values by injecting messages with a sufficiently large frame counter value and invalid payload. This results in denial of service/valid packets in the network. There is also a possibility of a replay attack in the stack.
- Affected products: version 6.5 of MiWi software and all previous versions, including legacy products.
- Vulnerability function and file: bool MiMAC_ReceivedPacket(void) function in mimac_at86rf.c file.
- Impact: an attacker may increment the incoming frame counter values by injecting messages with a sufficiently large frame counter value and invalid payload, which results in denial of service in the network. Protection against replay attacks is also not complete in the stack.
- Vulnerability fix details: this vulnerability is fixed in version 6.6 of MiWi software and the package is available.
In the code snippet below, the frame counters were validated/considered before the payload authentication.
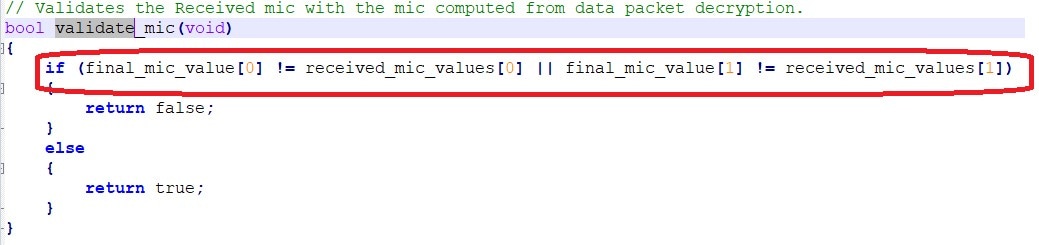
Validation of Only Two Out of Four MIC Bytes
In version 6.5 of our MiWi software and all previous versions including legacy products, the stack is validating only two out of four Message Integrity Check (MIC) bytes.
- Affected products: version 6.5 of MiWi software and all previous versions including legacy products.
- Vulnerability function and file: bool validate_mic(void) function in mimac_at86rf.c file.
- Impact: this vulnerability might allow someone to break in using brute force attacks.
- Vulnerability fix details: this vulnerability is fixed as part of version 6.6 of MiWi software; the package is available.
In the code snippet below, only two out of four MIC bytes were used.
Credits
Special thanks to Szymon Heidrich of Carrier Global Corporation for reporting this vulnerability.