TrustFLEX ATECC608 Secure Element for AWS® IoT Core Secure Authentication
Start with the Most Popular Pre-Configured Use Cases and Use Your Own Credentials
Benefits and Use Cases

Benefits of Using the TrustFLEX ATECC608 with AWS IoT Core
- Create secure authentication to IoT devices powered by AWS IoT Core
- Benefit from the scalability of AWS IoT Core (including China)
- Leverage AWS Thingpress
- Provide a unique, trusted, protected and managed device identity
- Pre-configured with most popular use cases
- Turn-key code examples available for each use case
- Leverage Microchip’s secure provisioning service
- Simplify logistics of shipping private keys and reduce manufacturing costs
- Microcontroller-agnostic implementation
- JIL rated “high” secure key storage
- Protection against known tamper, side-channel attacks

TrustFLEX ATECC608C-TFLXTLS Use Cases
Each of the device slots are pre-configured to offer the following use cases:
- Custom Certificate Authentication
- Token Authentication
- Secure Boot (with key attestation)
- Over-the-Air (OTA) Verification
- Firmware Intellectual Property (IP) Protection
- Message Encryption
- Key Rotation
- I/O Protection Key
- Host Accessory Authentication
Take Advantage of AWS Thingpress
Thingpress is a tool that makes AWS IoT device onboarding fast and easy. Many IoT devices use pre-provisioned x.509 certificates for secure authentication. Manufacturers inject these certificates into secure chips during production—but they still need to be registered with AWS IoT.
Thingpress automates this process at scale by importing hundreds of thousands (or even millions) of certificates per day. It allows Trust&GO users to drag and drop the manifest file delivered with each purchase of Integrated Circuits (ICs) into their AWS environment in a properly set up S3 bucket. A cloud-formation script is provided to illustrate the implementation. Typically, the batch uploads approximately 100,000 certificates per hour, including all requested object associations.
More than certificate import:
- Creates an AWS IoT thing based on the Certificate Name (CN) value
- Links the certificate to the thing
- Optionally attaches:
- AWS IoT policy for authorization
- Thing type for fleet management
- Thing group for organizing devices
These associations help align with your application design and device lifecycle goals.
Check out the Getting Started section for step-by-step guidance.
Ready to Get Started With TrustFLEX and AWS IoT Core?
Step 1: Download the Trust Platform Design Suite (TPDS), available for Windows® and macOS®, to prototype with your secure element.
Step 2: Buy the development kit of your choice, then prototype and integrate your application code in the microcontroller.
Step 3: Once the C code is working in your embedded application, you are ready to create the configuration file using the TrustFLEX configurator that is available in the Design Suite. After the configuration file is finalized, submit a support ticket to obtain your encryption key. Encrypt the configuration file using the provided utility, load it in the support ticket and you will receive provisioned validation devices by our Hardware Secure Module (HSM) equipped factories.

Tools and Software
- Demo & Evaluation Boards
- Development Environment
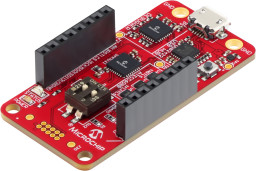
The CryptoAuth Trust Platform provides a compact development solution for developing IoT solutions with the ATECC608B-TNGTLS and ATECC608B-TFLXTLS and ATECC608B-MAHDA devices or the ATECC608C equivalents.
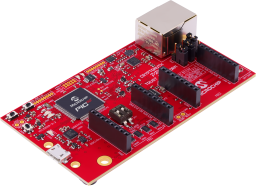
The Microchip CryptoAuth Pro Trust Platform is an enhanced version of the CryptoAuth Trust Platform Board containing and has a Arm® Cortex®-M4F Microcontroller, four on-board CryptoAuthentication devices, two mikroBUS™ sockets, and an on-board 10/100 Mbit Ethernet phy. Programming can be done via the on-board PKoB4 debugger which is compatible with MPLAB®X IDE. The board has been developed to work with Microchip's Trust Platform Development Suite of tools.
The Trust Platform Design Suite (TPDS) is our onboarding tool for our security-related solutions. The full onboarding experience includes, but is not limited to:
- Training and education about security concepts
- Prototyping, including dummy key generation and code examples, available via our interactive application notes
- Access to our provisioning system through a secure sub-system configurator and secure exchange process

MPLAB X IDE is a highly configurable software platform that provides powerful, free tools for developing, debugging and qualifying embedded designs that use microcontrollers and digital signal controllers.