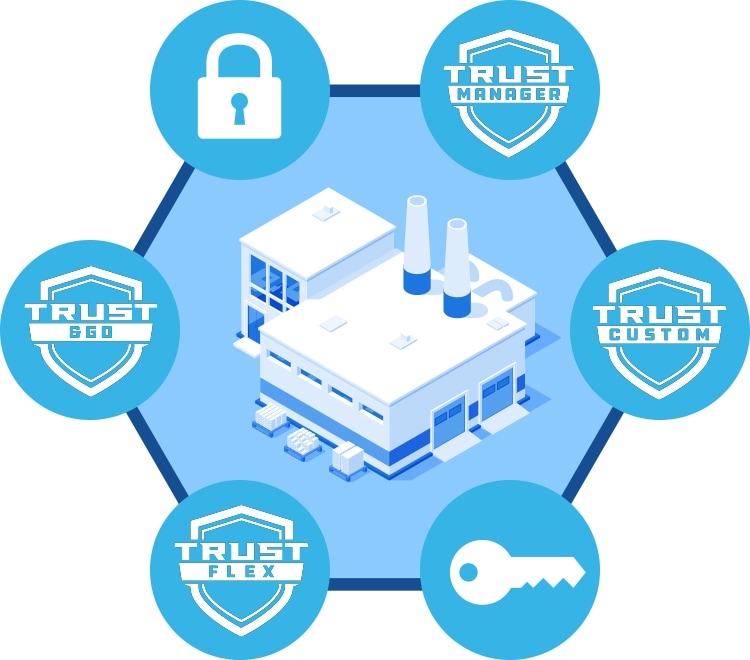
Trust Platform
Flexible and Easy Provisioning for Trusted Device Security

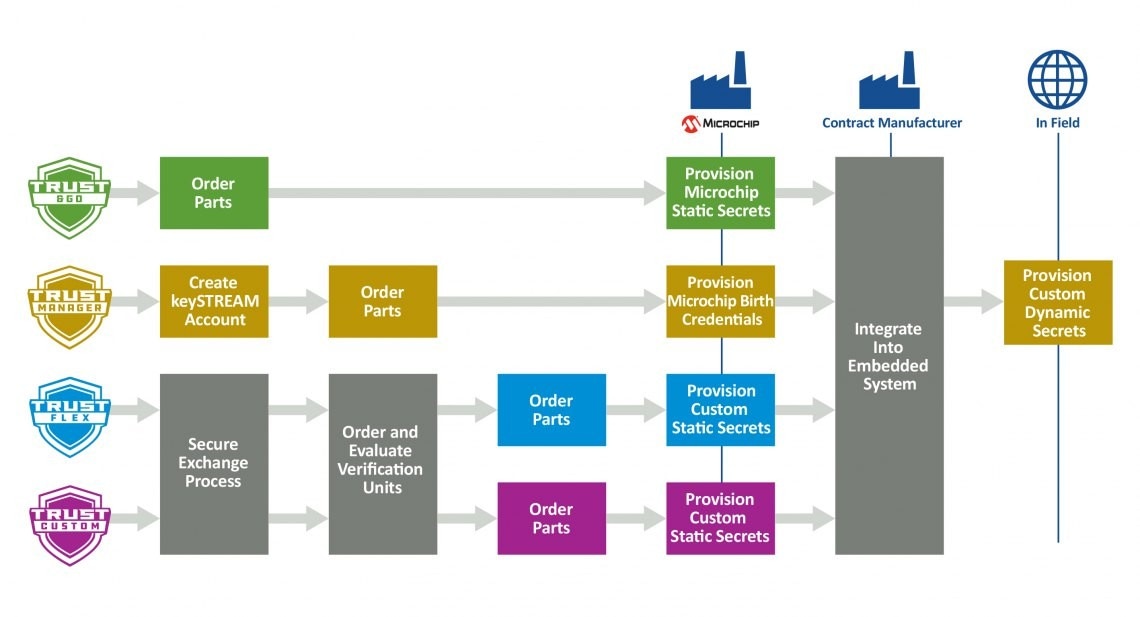
Trust&GO
Out-of-the-box security solution pre-provisioned with Microchip keys and certificates for TLS use cases. Ideal for quick deployment with no secret exchange required.
- ATECC608-TNGTLS

TrustMANAGER
Key management system (KMS) with dynamic key and certificate management, supporting in-field provisioning, FOTA and code signing. Designed for scalable, secure IoT deployments.
- ECC608-TMNGTLS
- TA101-TMNGTLS

TrustFLEX
Versatile platform with pre-configured use cases and broad device support. Requires secret exchange and offers code examples for each supported configuration.
- Select secure ICs, PRoT Controllers and MCUs

TrustCUSTOM
Fully customizable security IC platform starting from a blank device. Ideal for tailored use cases with full control over provisioning and configuration.
- All secure ICs, PRoT Controllers and MCUs
TA101 TrustMANAGER and TrustFLEX Early Adopter Program
Get early access to TA101‑TFLX (TrustFLEX) and TA101‑TMNG (TrustMANAGER) beta silicon devices.
TA101‑TFLX is a robust secure key storage device paired with a set of predefined security protocols for teams who want to integrate TA101 into their own public key infrastructure (PKI) systems.
TA101‑TMNG includes the same key storage and protocol capabilities, but adds the keySTREAM cloud platform for remote configuration, PKI creation, key management, and firmware updates —removing the burden of building a managed IoT security infrastructure in‑house.

Why Choose Our Provisioning Services?
In manufacturing, without secure key provisioning, sensitive keys face exposure to third-party software, microcontroller (MCU) firmware, contract manufacturers and operators. Given the elevated risks in mass production, it's crucial to securely store credentials using a process aligned with good security practices. Our Trust Platform provisioning service aims to isolate credentials from exposure during and after production, making it possible to handle keys securely.
The image below shows the steps to provision devices for production with each tier of the Trust Platform, which offers varying levels of complexity and customization.
Product Families
Secure Authentication ICs
Dedicated hardware security ICs that deliver tamper‑resistant key storage, cryptographic services and strong device authentication to protect systems, identities and data. These devices help prevent counterfeiting, enable secure communications such as TLS, and support secure firmware updates (FOTA), establishing a hardware root of trust for robust, end‑to‑end system protection.
Platform Root of Trust Controllers
Dedicated controllers that establish a resilient chain of trust from first power‑on. Designed to meet evolving mandates such as CNSA 2.0, CRA, NIST SP 800‑193 and OCP, with PQC‑ready architectures to protect platforms across boot, runtime and firmware updates.
Microcontrollers
Microcontrollers with built‑in security features that combine application processing with hardware‑based protection for secure system operation.
Ready to Start Development?
To prototype security use cases with development kits, use the tutorials and code examples within the Trust Platform Design Suite (TPDS) software, which is available for Windows® and macOS® operating systems.
When working on custom configurations through TrustFLEX and TrustCUSTOM, request verification units by submitting the secure exchange questionnaire from TPDS and ordering verification units through microchipDIRECT.

Secure Key Provisioning Factory Certifications
Avoid the high risks of exposing your secret keys and reduce the costs of mass production by leveraging our secure key provisioning service. Our Trust Platform provisioning service prevents your credentials from being exposed at any time during product development and production while also eliminating the need for you to have extensive knowledge and the necessary secure networks to handle cryptographic keys securely.
Our factories acheive these Common Criteria certifications:
- SLC_CMC.5
- ALC_CMS.5
- ALC_DVS.2
- ALC_LCD.1
- ALC_DEL.1
These site certifications ensure that we hold the processes in our supply chain to the highest standards.
Learn more about the certifications at our MPHIL-1 and MPHIL-3 factories in the Philippines and MTHAI-0 and MMT-0 factories in Thailand.
Our processes for designing automotive products have also been UL-certified as compliant to the ISO/SAE 21434: Road Vehicle—Cybersecurity Engineering Standard. This is a demanding specification with 45 security categories, known as work products, each of which specifies a unique set of requirements that encompass all aspects of designing electrical and electronic systems for road vehicles, from ICs and software to firmware and libraries. The ISO/SAE 21434 designation demonstrates that we are dedicated to maintaining high standards in automotive cybersecurity and that cybersecurity is a priority focus throughout our entire organization.
Still Not Sure How To Get Started?
- To help with your configuration setup and transaction diagram, we handpicked a team of trusted design partners that offer their expertise to guide you along the way. They will also help with your project development from use case definition all the way through to production.
- If you need more information about our secure elements, please visit our CryptoAuthentication™ ICs page.