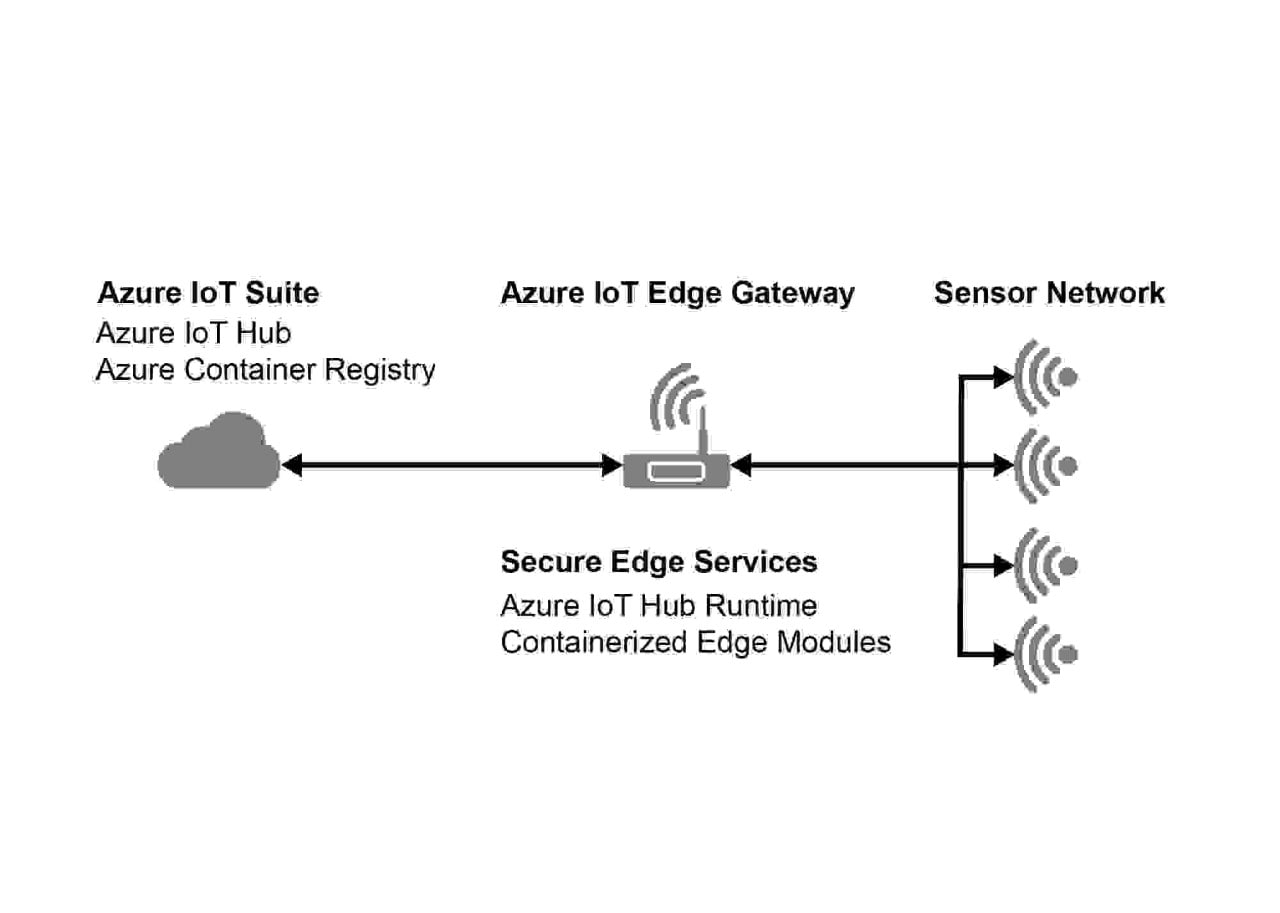
Create highly-secured design with our Microsoft Azure Certified intelligent edge solution based on the SAMA5D2 micrprocessor (MPU). This secured solution environment allows the edge gateway device to be authenticated as part of the Azure cloud. This combination of hardware and software security provided by Microchip and Sequitur Labs enables the deployment of secured gateways certified for the Microsoft Azure ecosystem to prevent potential theft or loss of data.
Why Use This Solution?
With our Azure solution, you can provide a secure intelligent edge gateway for Azure to your customers. The ample security features leveraged by the Sequitur Labs IoT Security Suite and the SAMA5D2 MPU will keep your secrets secure and your IP, revenue and customers protected.
- Establish the intelligent edge as a root of trust
- Reduce operating cost
- Mitigate connectivity outages
- Secure connectivity
- Intellectual property protection
- Keys/certificates protection
- Secure boot/secure update
- Trusted Execution Environment (TEE)
- Docker® technology supported
Trusted Partnership
Security
Microsoft Azure Gateway Solution
Sequitur IoT Suite
With the IoT Security Suite for the SAMA5D2 MPU, you can implement security functions that are foundational to trustworthy IoT devices. These include implementing hardware-based isolation, access to hardware cryptography and implementing a hardware-based root-of-trust as well as essential key and certification management tools.
